The Of Risk Management Enterprise
Our Risk Management Enterprise PDFs
Table of ContentsRisk Management Enterprise Fundamentals ExplainedThe Definitive Guide for Risk Management EnterpriseThe Ultimate Guide To Risk Management EnterpriseRisk Management Enterprise Fundamentals ExplainedAn Unbiased View of Risk Management EnterpriseAn Unbiased View of Risk Management EnterpriseThe Main Principles Of Risk Management Enterprise
Below are several of its key functions that centers need to recognize. So, take an appearance. Real-Time Danger Analyses and Reduction in this software application enable companies to constantly keep track of and review risks as they develop. This attribute leverages real-time data and computerized evaluation to identify potential risks immediately. Once dangers are recognized, the software assists in prompt reduction activities.
KRIs address the problem of irregular or vague threat evaluation. They address the obstacle of continuous risk administration by offering devices to keep an eye on threats continually. KRIs improve safety and security danger oversight, ensuring that potential risks are identified and managed properly. The job of risk administration must not be a difficulty. As a result, organizations should rely upon a superior and innovative danger administration software application.
The 2-Minute Rule for Risk Management Enterprise
IT risk monitoring is a subset of venture risk monitoring (ERM), made to bring IT run the risk of in accordance with a company's risk hunger. IT risk monitoring (ITRM) includes the plans, procedures and modern technology required to minimize hazards and vulnerabilities, while keeping compliance with relevant regulatory needs. In addition, ITRM looks for to limit the effects of harmful occasions, such as security breaches.
While ITRM structures offer beneficial assistance, it's easy for IT teams to struggle with "framework overload." Veronica Rose, ISACA board director and an info systems auditor at Metropol Corp. Ltd., advises using a mix of frameworks to achieve the most effective results. For example, the ISACA Risk IT structure lines up well with the COBIT 2019 framework, Rose said.
Venture Threat Monitoring Software Program Growth: Perks & Features, Expense. With technological improvements, risks are continuously on the surge., services browse with a frequently transforming sea of threats.
The smart Trick of Risk Management Enterprise That Nobody is Discussing
In this blog, we will certainly dive into the world of ERM software, exploring what it is, its benefits, functions, etc to ensure that you can develop one for your organization. Enterprise Danger Monitoring (ERM) software program is the application program for preparation, directing, organizing, and regulating business tasks and improving danger monitoring processes.
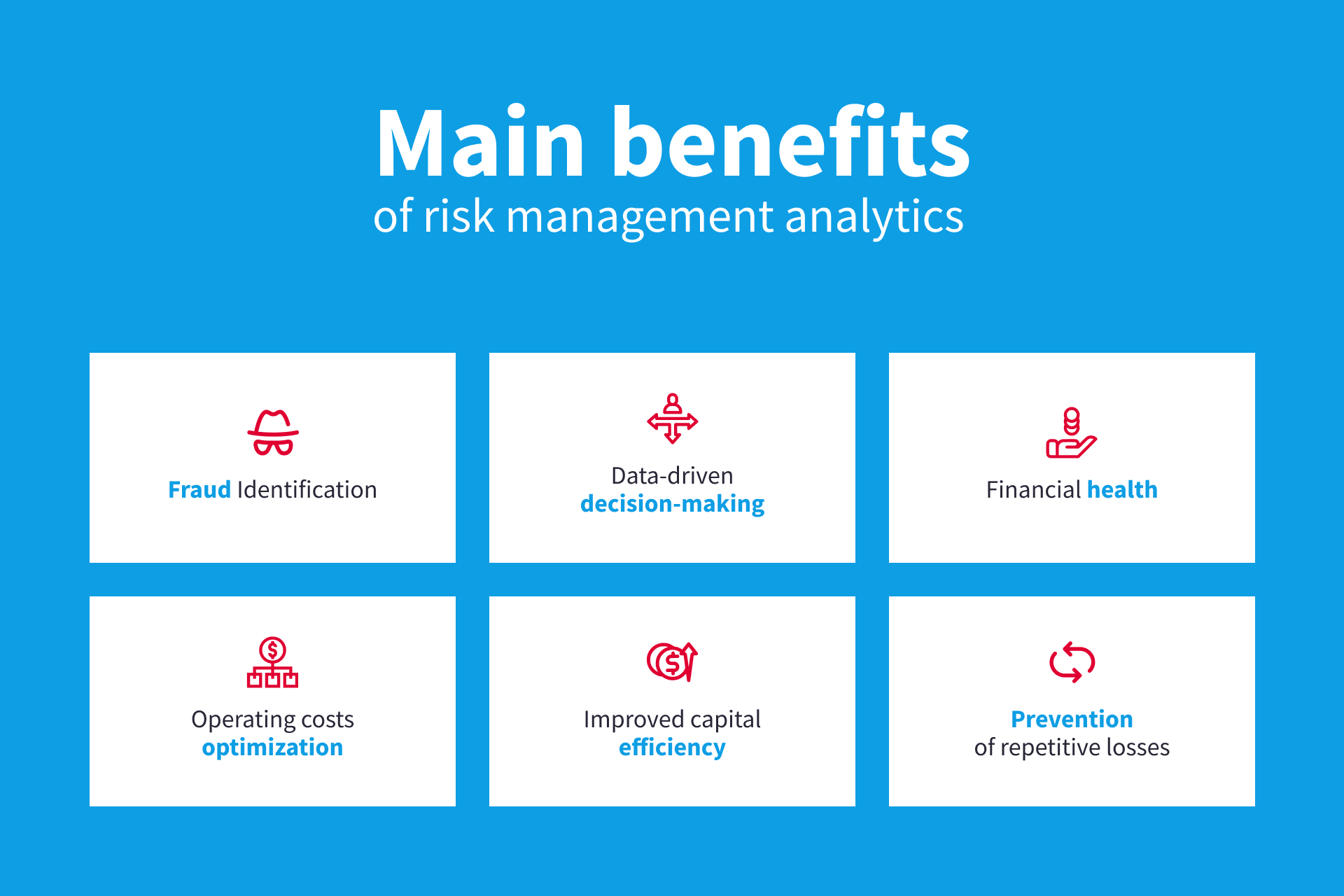
With ERM, companies can make insightful decisions to enhance the total strength of the business. Read: ERP Application Growth Dedicated ERM systems are critical for services that regularly handle huge quantities of delicate info and several stakeholders to authorize calculated choices. Some industries where ERM has become a common system are medical care, money, construction, insurance, and infotech (IT).
It can be stayed clear of by utilizing the ERM software application system. This system automates guideline conformity management to keep the organization protected and compliant.
A Biased View of Risk Management Enterprise
You can also connect existing software application systems to the ERM using APIs or by including information manually. Businesses can use ERM to assess risks based on their potential effect for better danger management and mitigation.: Including this attribute allows users to obtain real-time notifications on their tools about any threat that might occur and its effect.

Instead, the software permits them to establish limits for various procedures and send out press notifications in instance of possible threats.: By incorporating information visualization and reporting in the customized ERM software, businesses can acquire clear insights about threat fads and performance.: It is obligatory recommended you read for companies to stick to industry conformity and regulative requirements.

These platforms make it possible for companies to carry out best-practice risk administration processes that align with industry criteria, supplying an effective, technology-driven method to identifying, examining, and mitigating risks. This blog checks out the benefits of automatic threat monitoring devices, the locations of danger monitoring they can automate, and the worth they give an organization.
Risk Management Enterprise Can Be Fun For Everyone
Teams can set up forms with the relevant fields and easily produce various types for different threat kinds. These risk assessment forms can be circulated for completion using automated operations that send out notices to the pertinent team to finish the types online. If kinds are not finished by the deadline, after that chaser emails are instantly sent by the system.
The control tracking and control testing process can additionally be automated. Firms can use automated process to send out regular control test alerts and personnel can enter the outcomes using on-line forms. Controls can additionally be checked by the software by establishing guidelines to send out notifies based upon control data kept in various other systems and spread sheets that is drawn into the system using API integrations.
Risk monitoring automation software application can additionally sustain with risk coverage for all levels of the enterprise. Leaders can check out records on threat exposure and control effectiveness with a range of reporting outputs consisting of fixed records, Power BI interactive reports, bowtie evaluation, and Monte Carlo simulations. The capacity to draw live reports at the touch of a button cuts out strenuous information manipulation tasks leaving risk groups with more time to examine the information and encourage business on the most effective training course of activity.
The need for efficient has never ever been much more important. Risk Management Enterprise. Organizations operating in affordable, fast-changing markets can not manage delays or inefficiencies in attending to prospective threats. Conventional threat management making use of hand-operated spreadsheet-based procedures, while familiar, frequently lead to fragmented data, time-consuming reporting, and an enhanced possibility of human mistake. Automating the risk management process with software application addresses these drawbacks.
Risk Management Enterprise Things To Know Before You Buy
This guarantees risk registers are constantly current and straightened with business objectives. Conformity is another vital motorist for automating risk management. Standards like ISO 31000, CPS 230 and COSO all give assistance around risk management finest methods and control structures, and automated threat administration devices are structured to line up with these needs helping companies to fulfill most typically made use of danger monitoring standards.
Seek threat software application platforms with an authorizations hierarchy to easily establish workflows for danger escalation. This functionality enables you to customize the sight for every user, so they only see the information relevant to them. Make certain the ERM software application supplies individual monitoring so click to read you can see who entered what data and when.
Seek out devices that supply task threat monitoring capabilities to manage your jobs and profiles and the linked threats. The advantages of adopting risk administration automation software extend far beyond performance.
About Risk Management Enterprise
While the instance for automation is engaging, applying a threat monitoring system is not without its obstacles. For one, data high quality is important. Automated systems count on precise, updated details to provide meaningful understandings. To conquer the challenges of page risk monitoring automation, organizations must purchase data cleansing and governance to guarantee a strong foundation for applying an automated system.
Automation in threat administration equips services to change their approach to risk and construct a stronger structure for the future (Risk Management Enterprise). The inquiry is no much longer whether to automate risk management, it's exactly how soon you can begin. To see the Riskonnect at work,
The answer typically lies in just how well risks are prepared for and handled. Project monitoring software program works as the navigator in the tumultuous waters of task execution, offering tools that recognize and evaluate dangers and develop techniques to alleviate them efficiently. From real-time information analytics to comprehensive risk tracking control panels, these devices give a 360-degree sight of the project landscape, allowing job managers to make informed choices that maintain their projects on track and within spending plan.